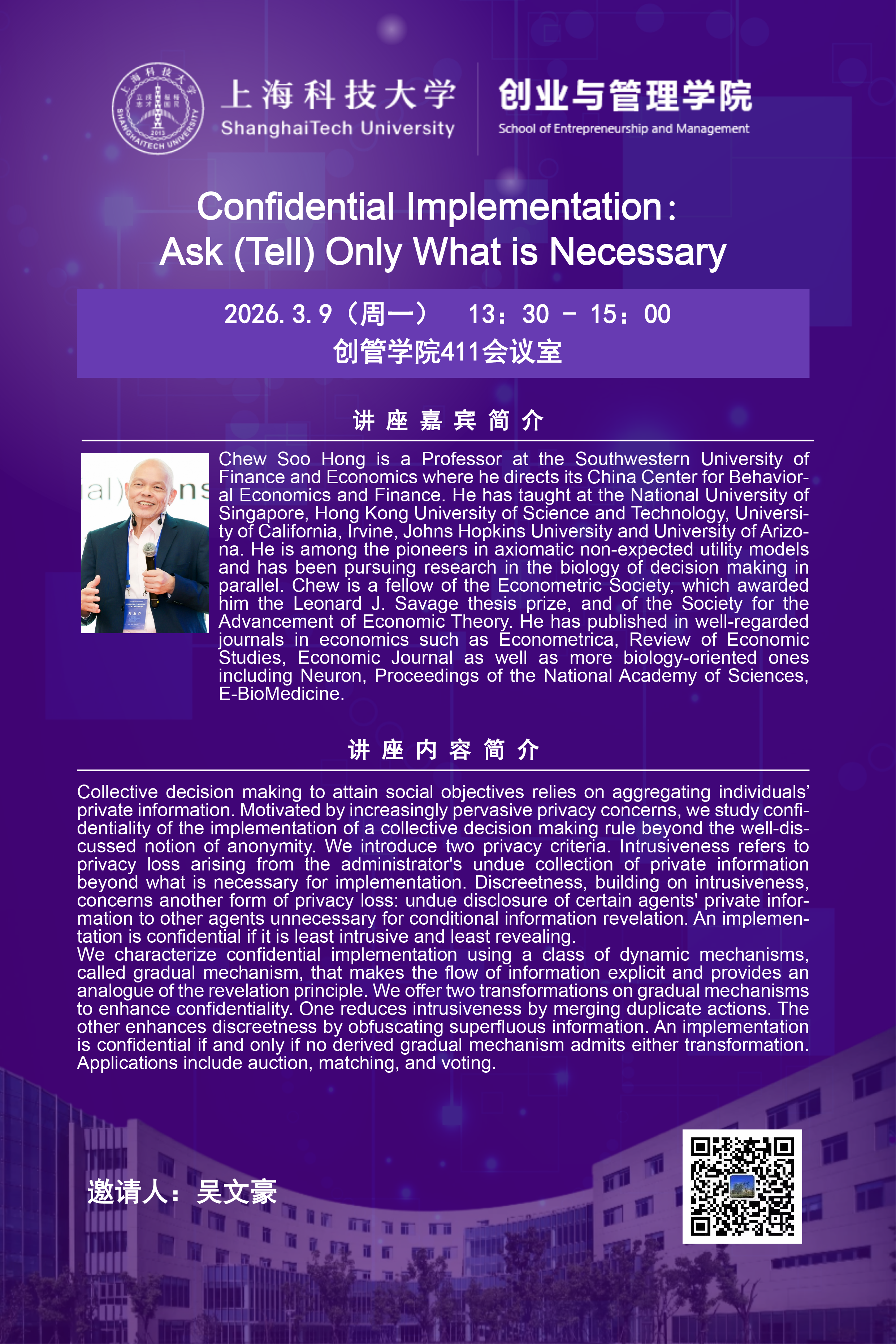
主讲人简介:Chew Soo Hong is a Professor at the Southwestern University of Finance and Economics where he directs its China Center for Behavioral Economics and Finance. He has taught at the National University of Singapore, Hong Kong University of Science and Technology, University of California, Irvine, Johns Hopkins University and University of Arizona. He is among the pioneers in axiomatic non-expected utility models and has been pursuing research in the biology of decision making in parallel. Chew is a fellow of the Econometric Society, which awarded him the Leonard J. Savage thesis prize, and of the Society for the Advancement of Economic Theory. He has published in well-regarded journals in economics such as Econometrica, Review of Economic Studies, Economic Journal as well as more biology-oriented ones including Neuron, Proceedings of the National Academy of Sciences, E-BioMedicine.
讲座简介:Collective decision making to attain social objectives relies on aggregating individuals’ private information. Motivated by increasingly pervasive privacy concerns, we study confidentiality of the implementation of a collective decision making rule beyond the well-discussed notion of anonymity. We introduce two privacy criteria. Intrusiveness refers to privacy loss arising from the administrator's undue collection of private information beyond what is necessary for implementation. Discreetness, building on intrusiveness, concerns another form of privacy loss: undue disclosure of certain agents' private information to other agents unnecessary for conditional information revelation. An implementation is confidential if it is least intrusive and least revealing.
We characterize confidential implementation using a class of dynamic mechanisms, called gradual mechanism, that makes the flow of information explicit and provides an analogue of the revelation principle. We offer two transformations on gradual mechanisms to enhance confidentiality. One reduces intrusiveness by merging duplicate actions. The other enhances discreetness by obfuscating superfluous information. An implementation is confidential if and only if no derived gradual mechanism admits either transformation. Applications include auction, matching, and voting.



 沪公网安备 31011502006855号
沪公网安备 31011502006855号